Enabling Azure AD SSO connections with your OVHcloud account
Find out how to associate your Azure Active Directory to your OVHcloud account using SAML 2.0
Find out how to associate your Azure Active Directory to your OVHcloud account using SAML 2.0
Last updated 5th April 2023
You can use Single Sign-On (SSO) to connect to your OVHcloud account. To enable these connections, your account and your Azure AD have to be configured using SAML (Security Assertion Markup Language) authentications.
This guide explains how to associate your OVHcloud account with an external Azure AD.
In order for a service provider (i.e. your OVHcloud account) to establish an SSO connection with an identity provider (i.e. your Azure AD), the essential part is to establish a mutual trust relationship by registering the SSO connection in both services.
Your Azure AD acts as your identity provider. Authentication requests by your OVHcloud account will only be accepted if it is declared as a trusted party first.
Let's focus for a moment on the identities on the identity provider side.
To start, go to your Azure AD dashboard.
Then click on Users from the left-hand menu.
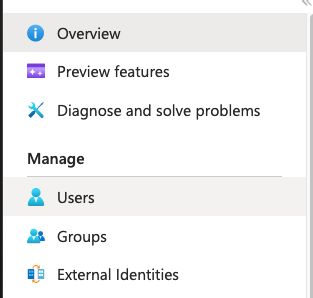
Create as many users as you need, or you can just check your users clicking on them.
For this example, the user John Smith will be used.
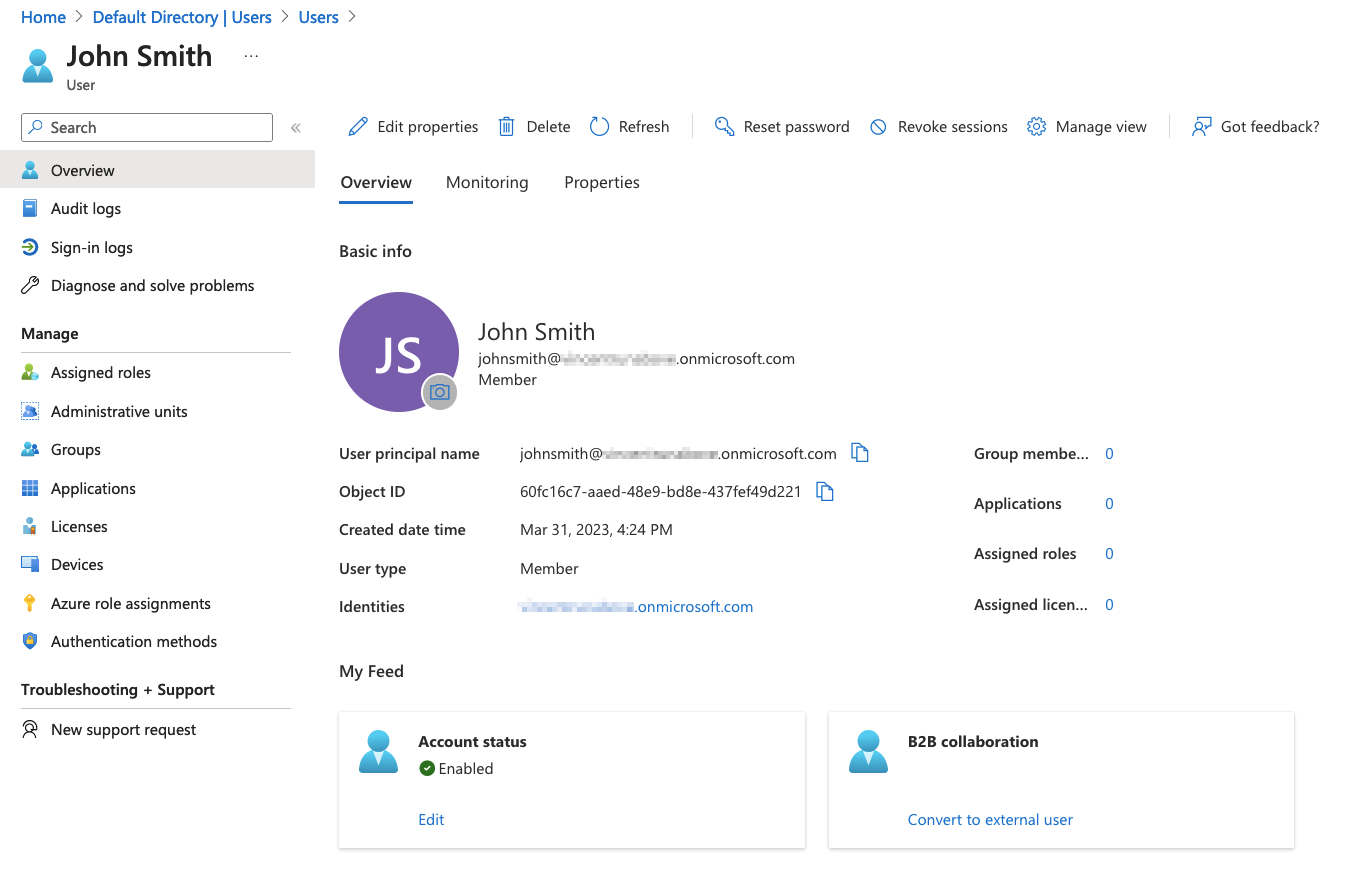
When an SSO authentication is performed, John Smith's identity will be provided by Azure AD to the OVHcloud account. However, it is necessary that this identity contains at least one group. If no group exists, let's look at how to create one to add John Smith to it.
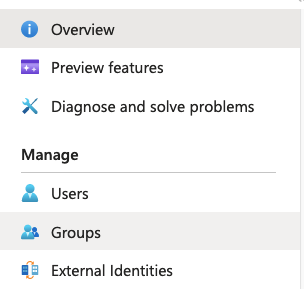
Click on Groups from the left-hand menu.
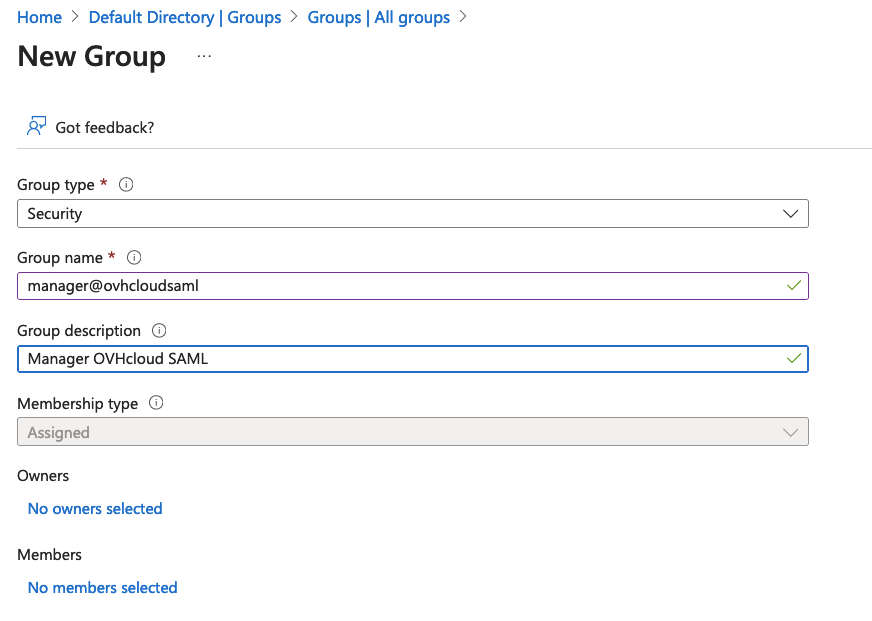
Click on New group in the top menu, and fill in all the necessary information.
For this example, the group manager@ovhcloudsaml will be used.
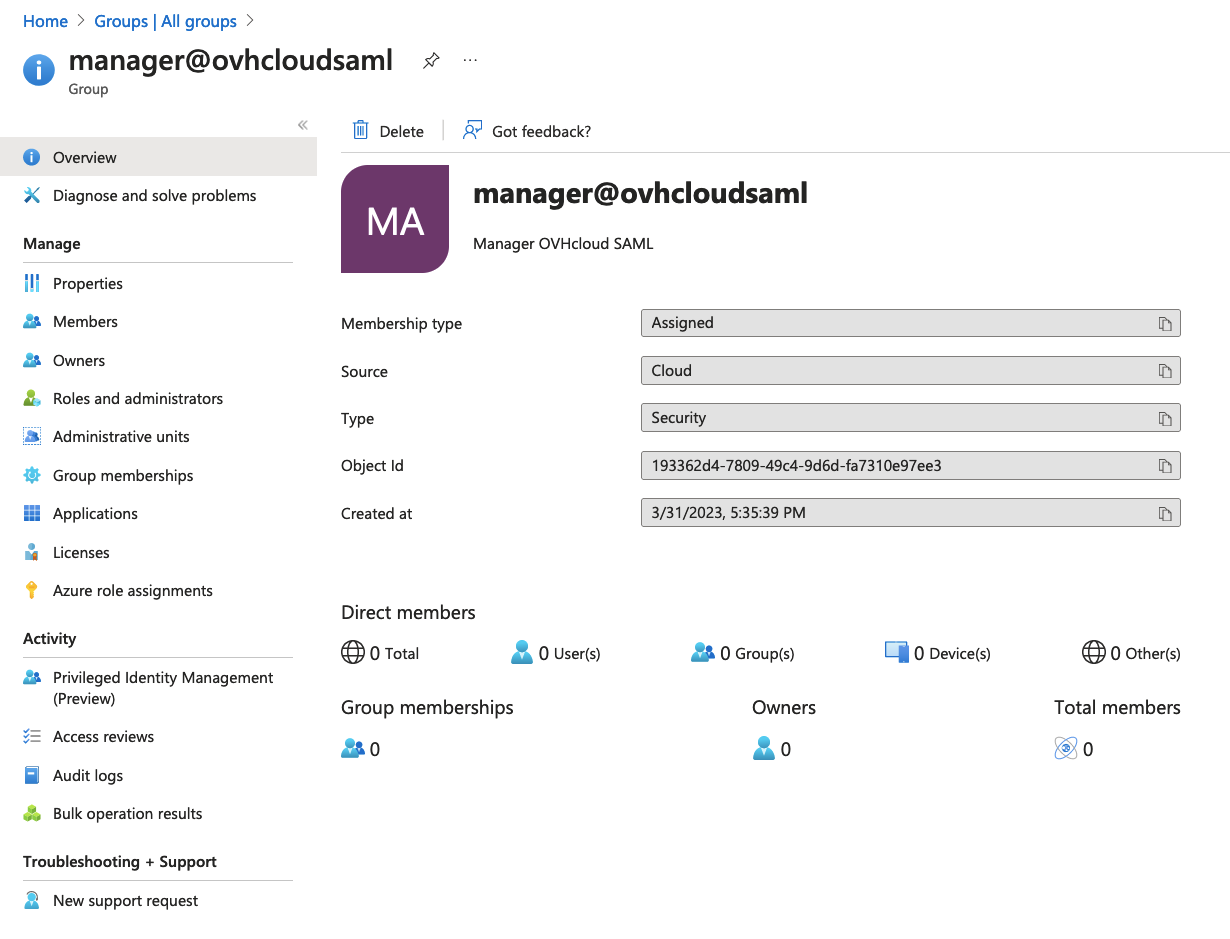
Click on the Create button to display all information about this group.
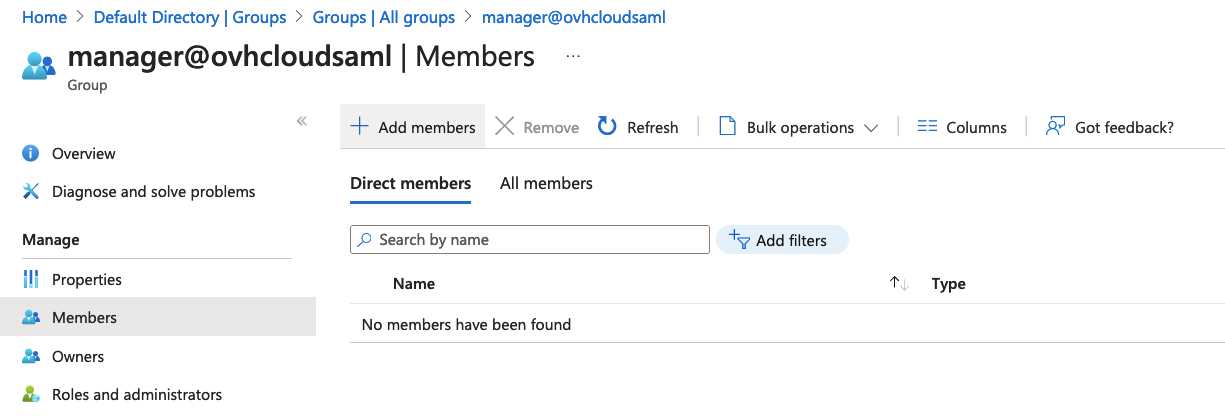
Now, users who will be used for SSO authentication must be added to a group.
In this example, let's link the user John Smith with the group manager@ovhcloudsaml.
In the selected group interface, click on Members from the left-hand menu, then click Add members in the top menu.
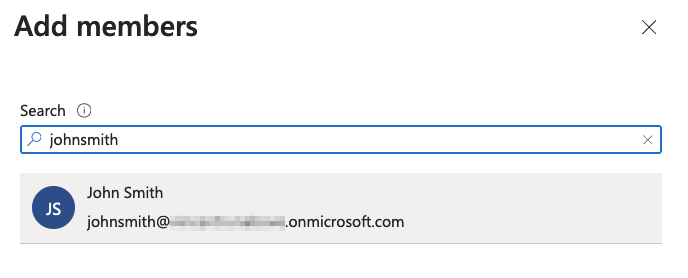
Select the user to be added to this group, then click on the Select button.
Now we have a user assigned to a group.
In order to perform SSO authentications, an Azure AD application must be created.
SSO must be configured on this application.
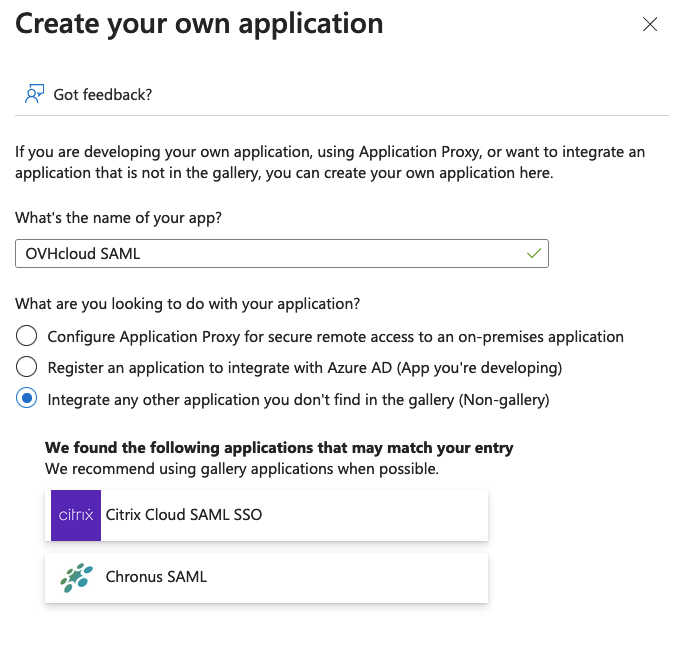
First of all, it is necessary to create an application if one does not yet exist.
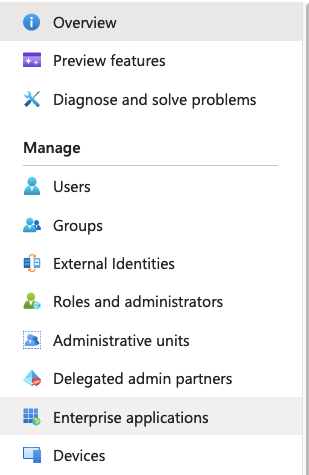
Click on Enterprise applications from the left-hand menu.
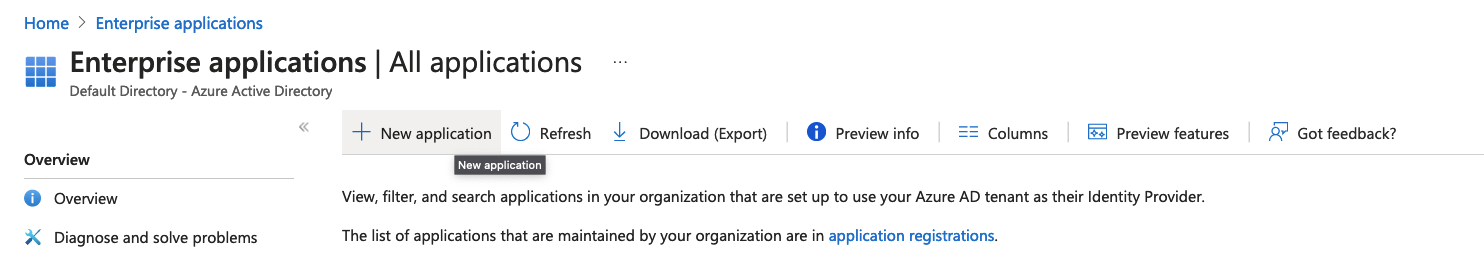
Click on New application in the top menu.
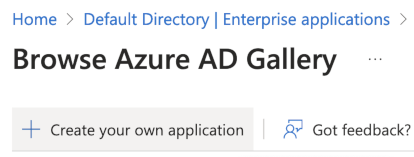
Click on Create your own application in the top menu.
Select the Non-gallery from the left-hand menu, and click on the Create button.
The details of the application will then be displayed.
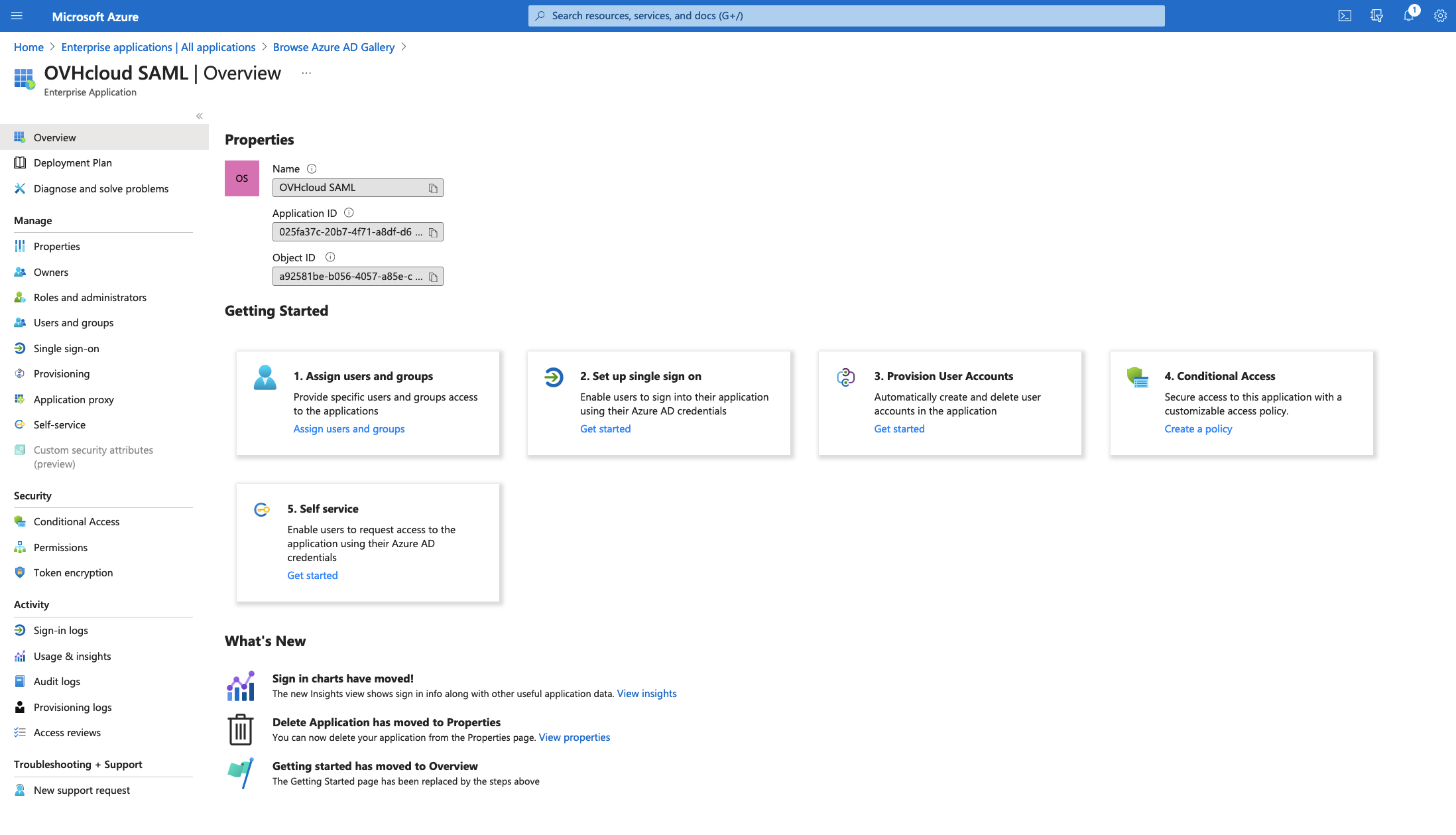
The Azure AD application is now created. Users who want to perform SSO authentications via this application must now be added to it.
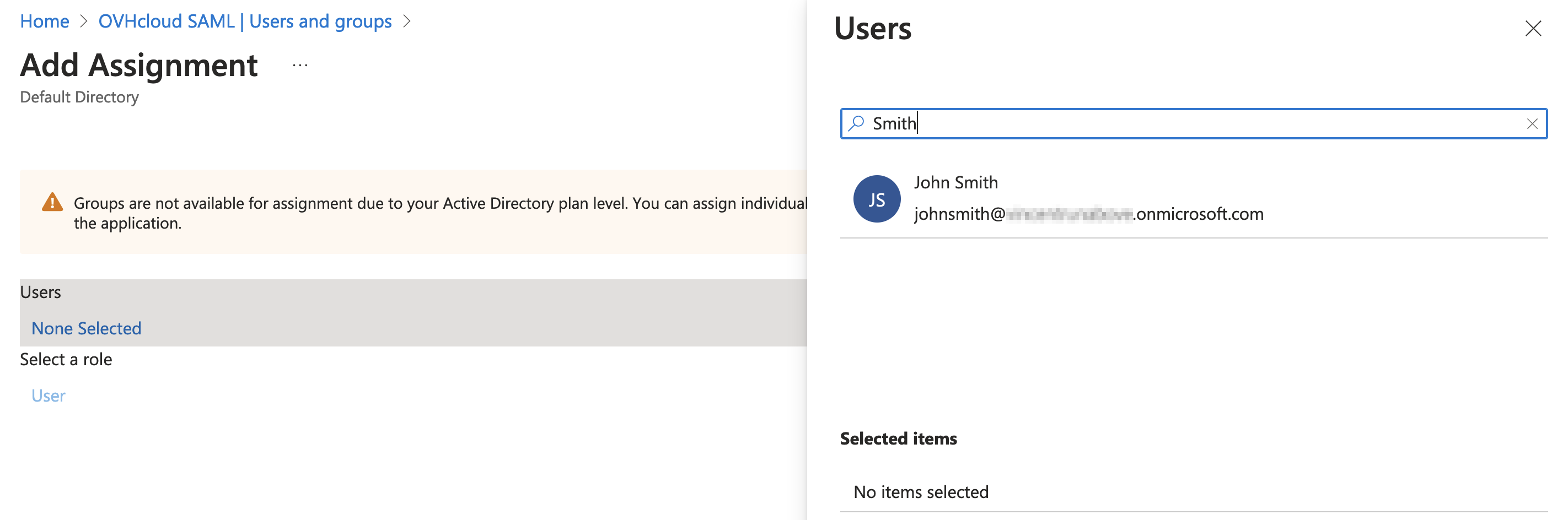
In order for a user to perform an SSO authentication from an Azure AD application, it must be added to that application. It is therefore shown here how to add a user to an Azure AD application.
However, it is better to add a user group instead of users if you have Azure AD Premium.
Click on Users and groups from the left-hand menu, then click Add user/group in the top menu.
Click then on the Users section, select the user to add to the application, and click on the Select button.
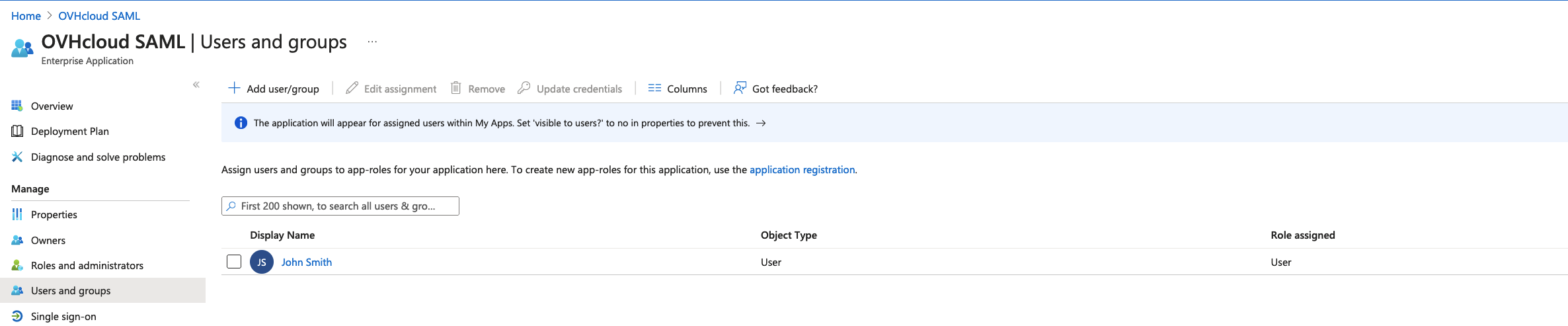
The application is created, a user has been assigned, all that remains is to set up the SSO via SAML.
Get back to the overview via the Overview button from the left-hand menu, then click on the Set up single sign on section.
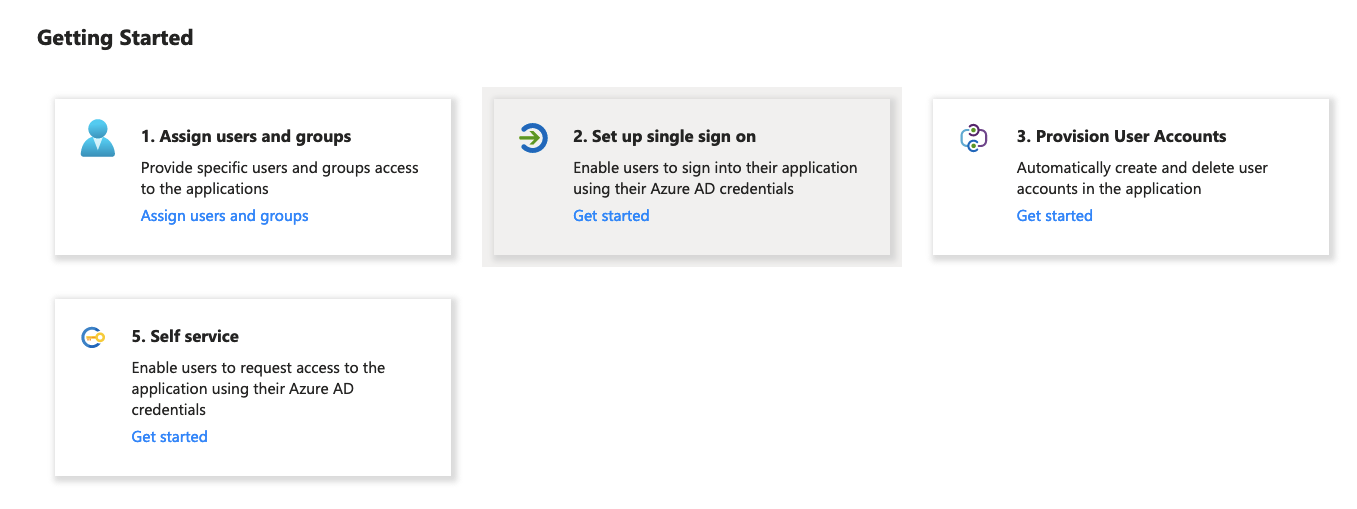
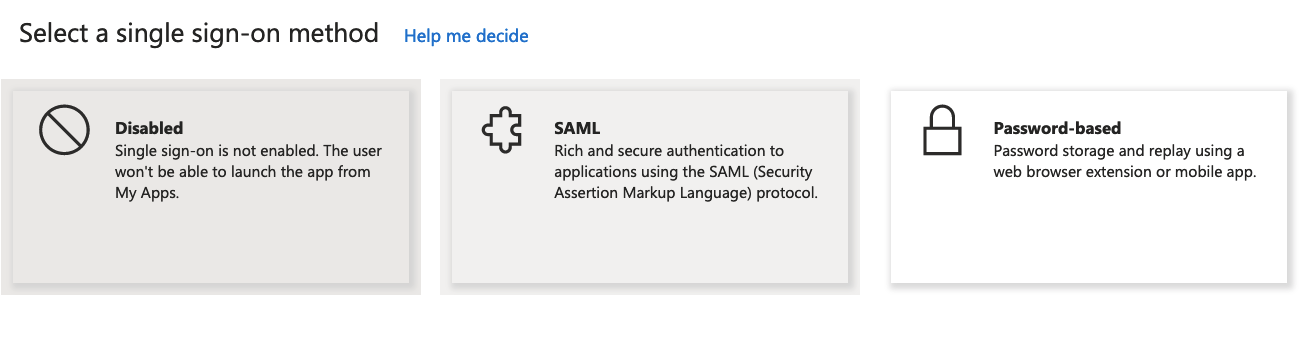
Click on the SAML section.
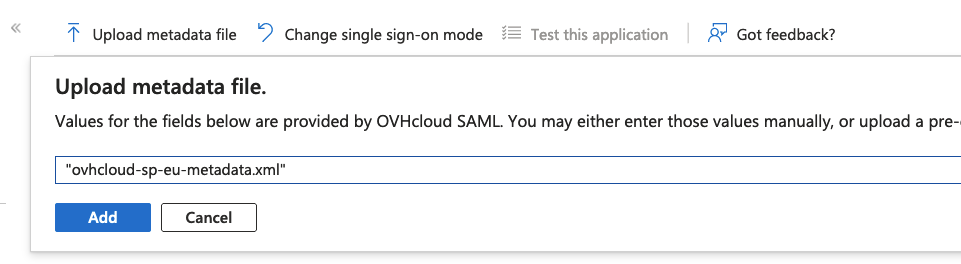
Click on Upload metadata file in the top menu.
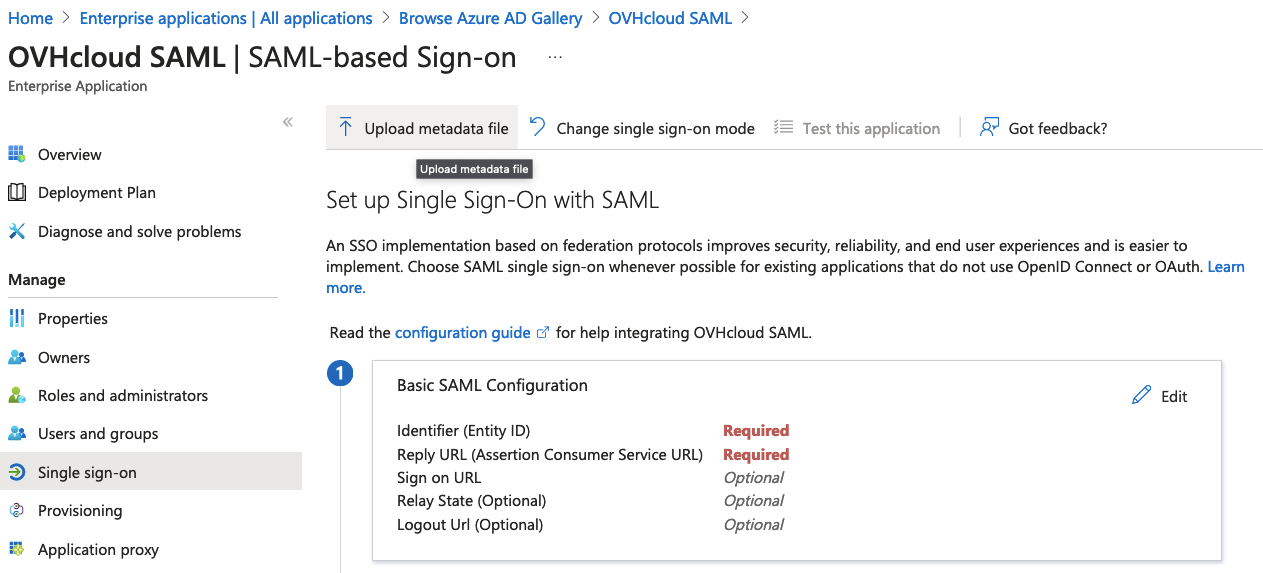
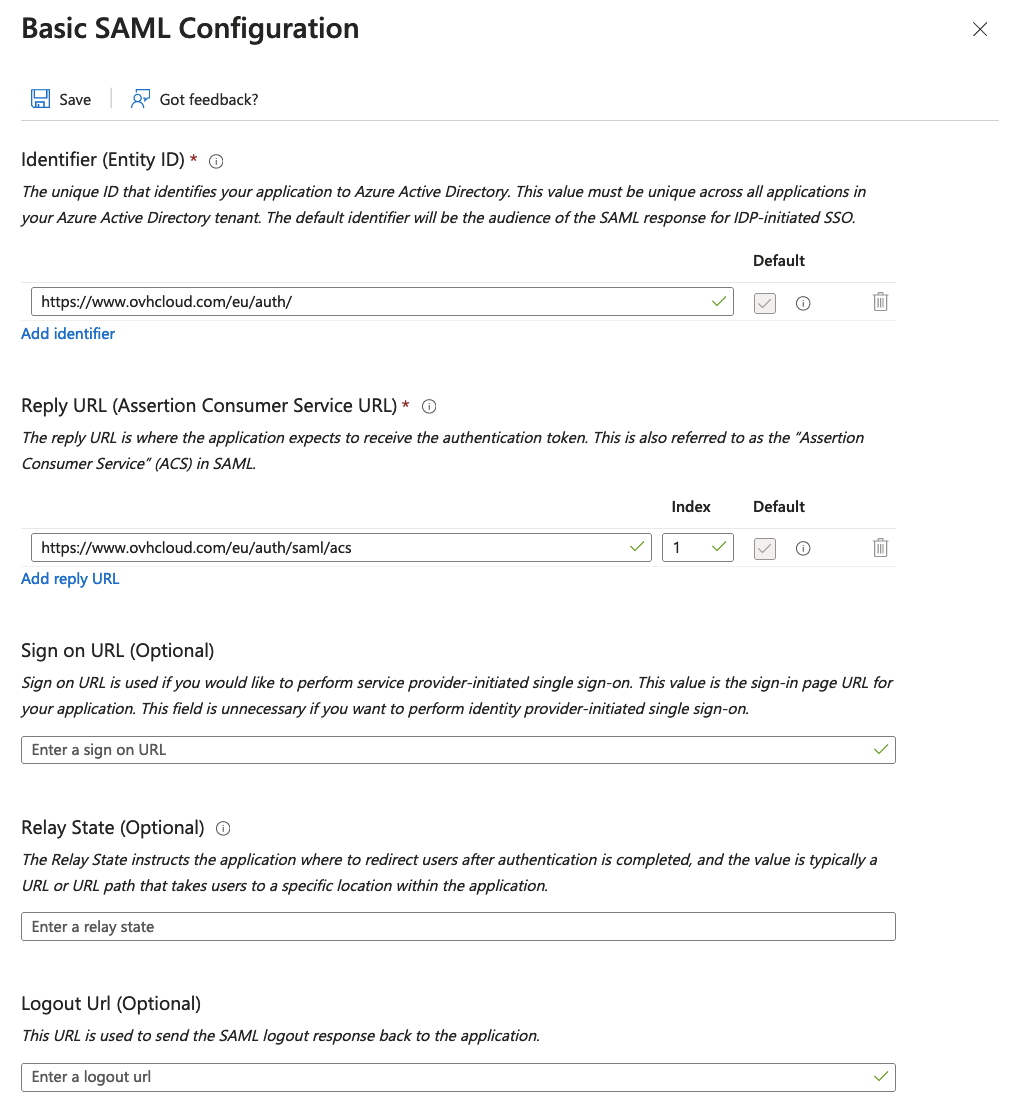
Click on the Select a file icon button, select the OVHcloud Service Provider metadata file and click on the Add button.
You can obtain the appropriate metadata file via the following links:
Download the metadata file, it will be necessary later.
The SAML configuration will be displayed.
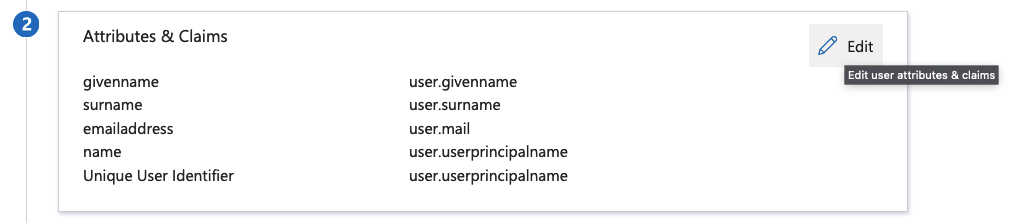
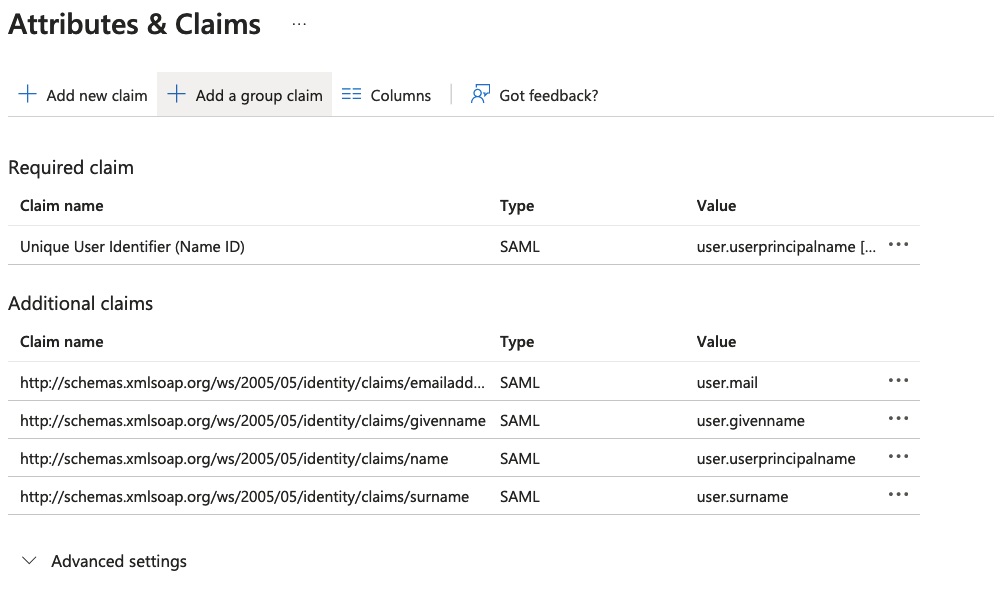
In the Attributes & Claims section, click on the Edit button.
Click on Add a group claim in the top menu.
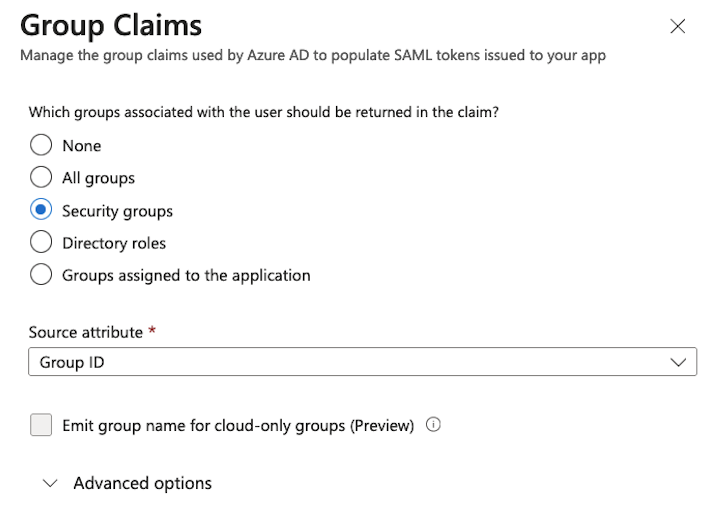
Select Security groups, and Group ID from the Source attribute and click on the Save button.
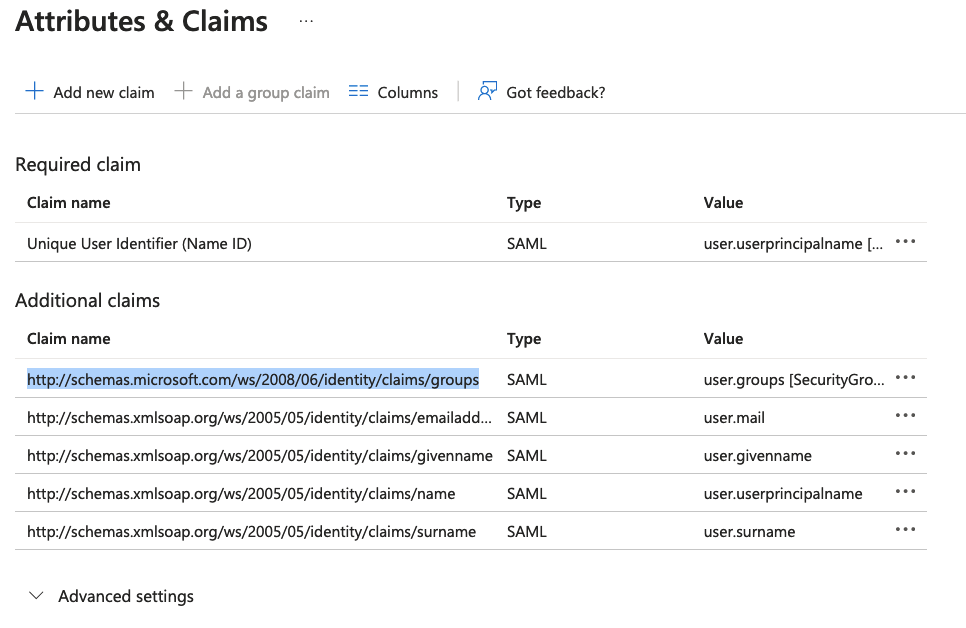
The groups claim should now appear in the list.
Copy and save the Claim name value somewhere (i.e a notepad), it will be necessary later.
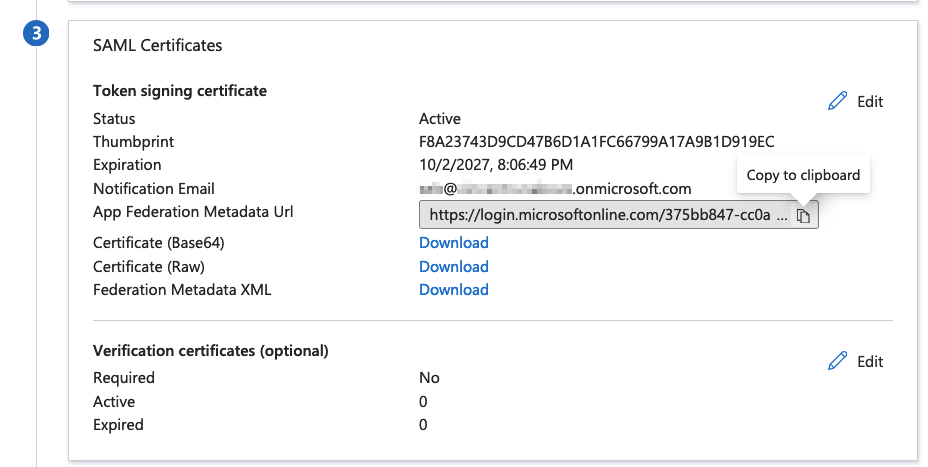
In the SAML certificates section, copy the App Federation Metadata Url field value.
Use this link to download the Azure AD application metadata file in order to use it later in the OVHcloud account.
Adding your Azure AD application as a trusted identity provider is done in the OVHcloud Control Panel where you can provide the identity provider metadata.
Log in and click on your profile in the top-right corner.
Click on your name to access your profile management page.
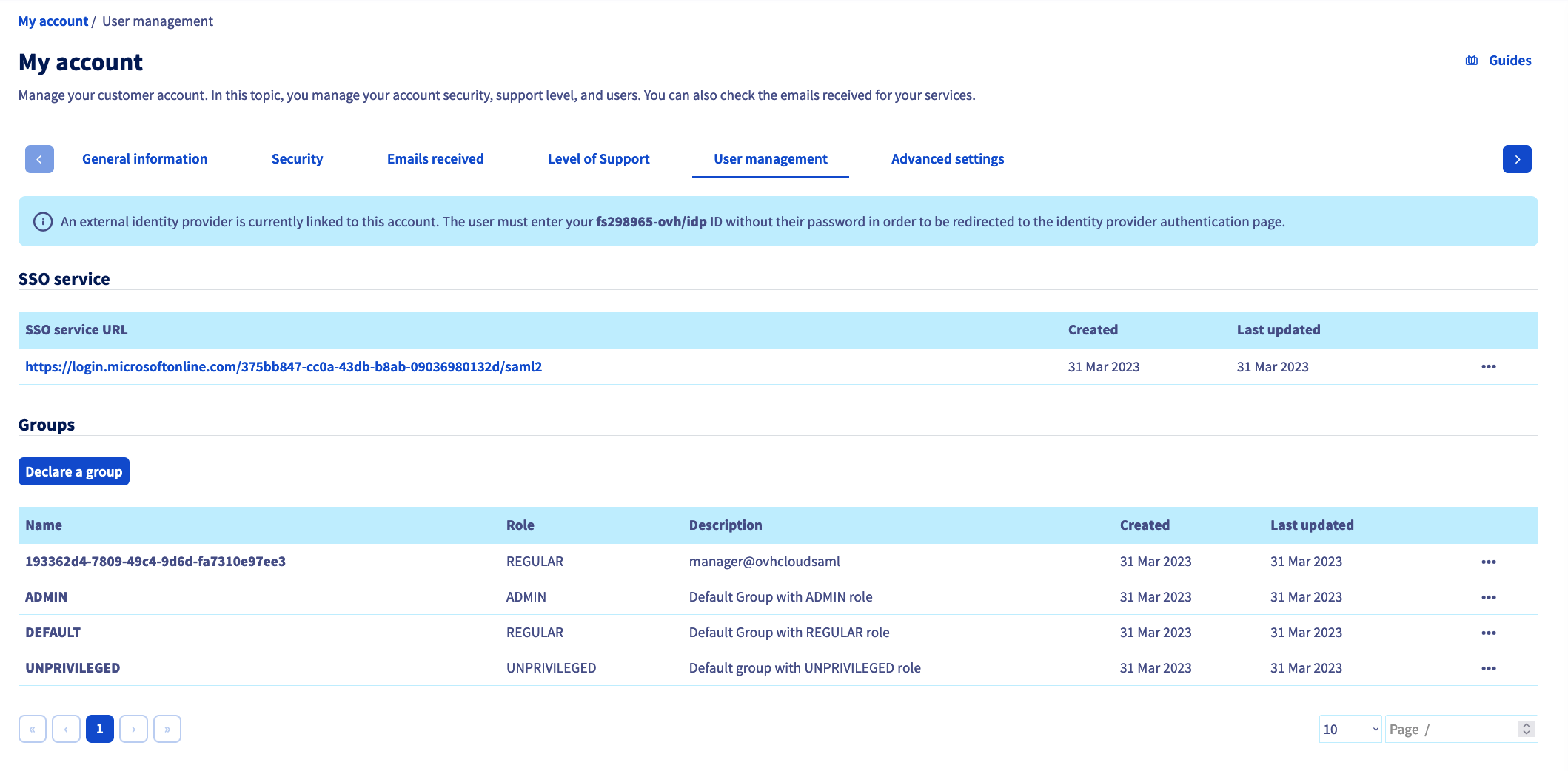
Open the User management tab.
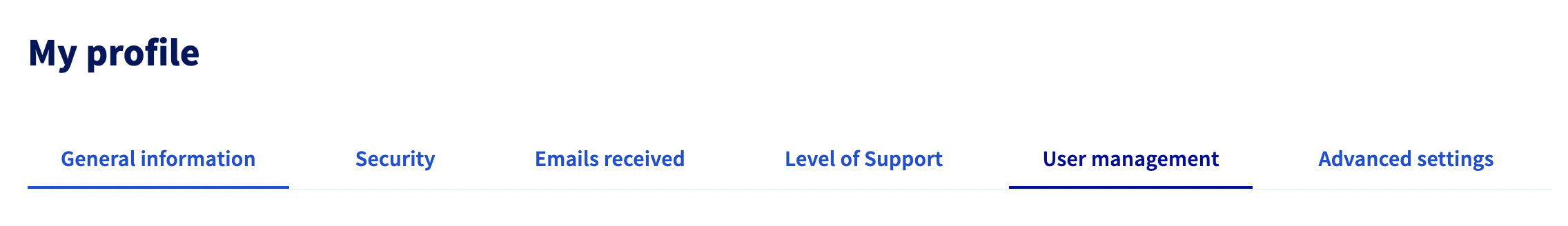
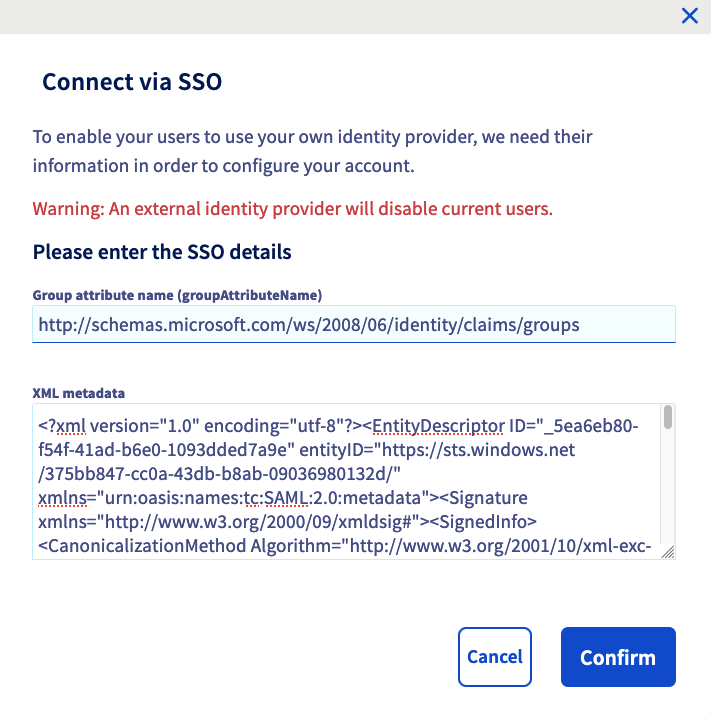
Click on the SSO connection button.
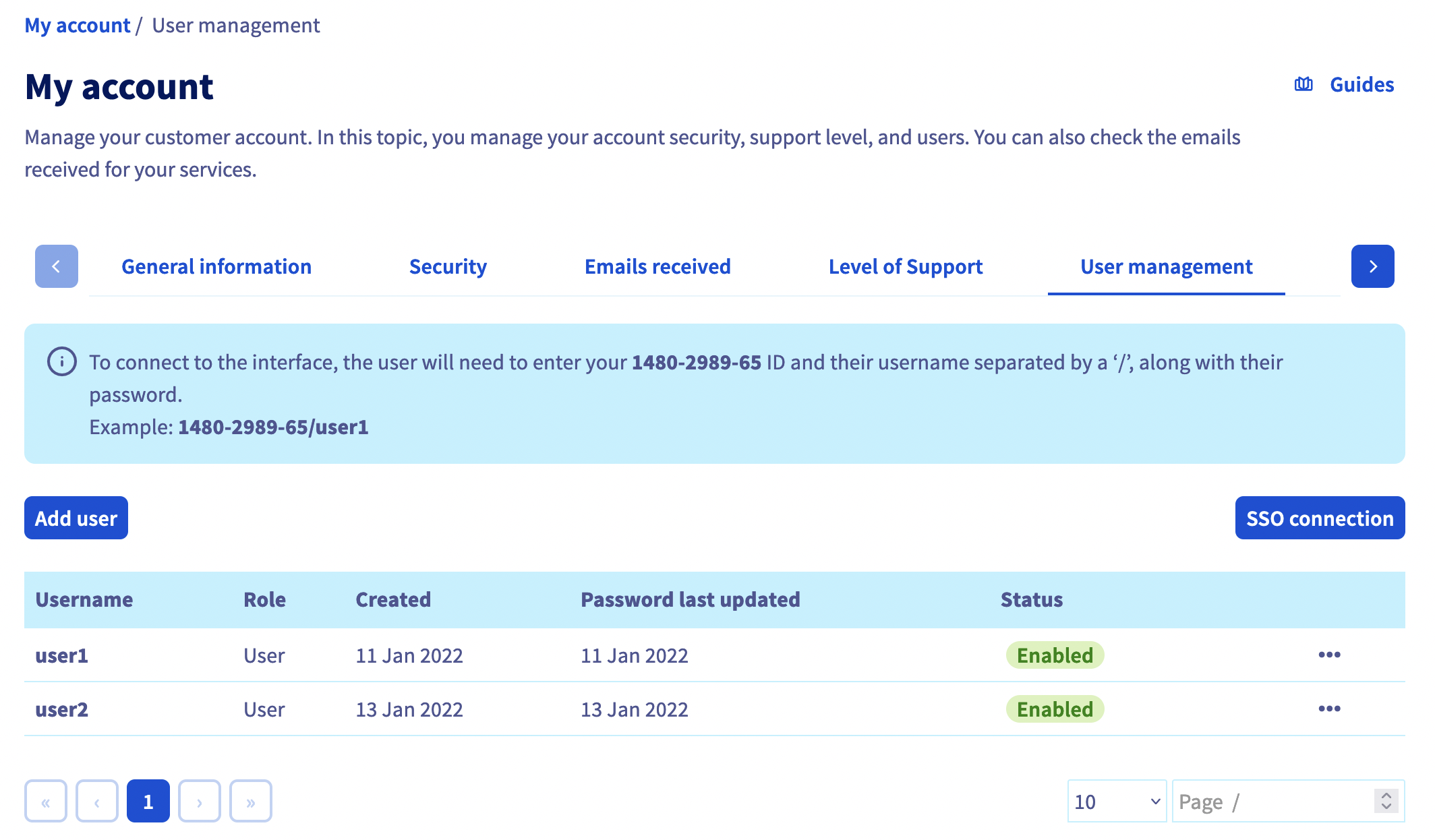
Fill in the Group Attribute Name field with the Azure AD application groups Claim name value saved before.
Fill in the XML metadata of your Azure AD application from the file saved before.
Click on the Confirm button.
The trust of your Azure AD application as identity provider is thus established but you still have to add groups to your OVHcloud account.
If you try to connect at this stage via SSO, you will probably receive a Not in valid groups error message.
That is because your OVHcloud account checks if the authenticating user belongs to a group that actually exists on the account.
To resolve this, check the "Group" attribute that your Azure AD application returns: the Object Id field.
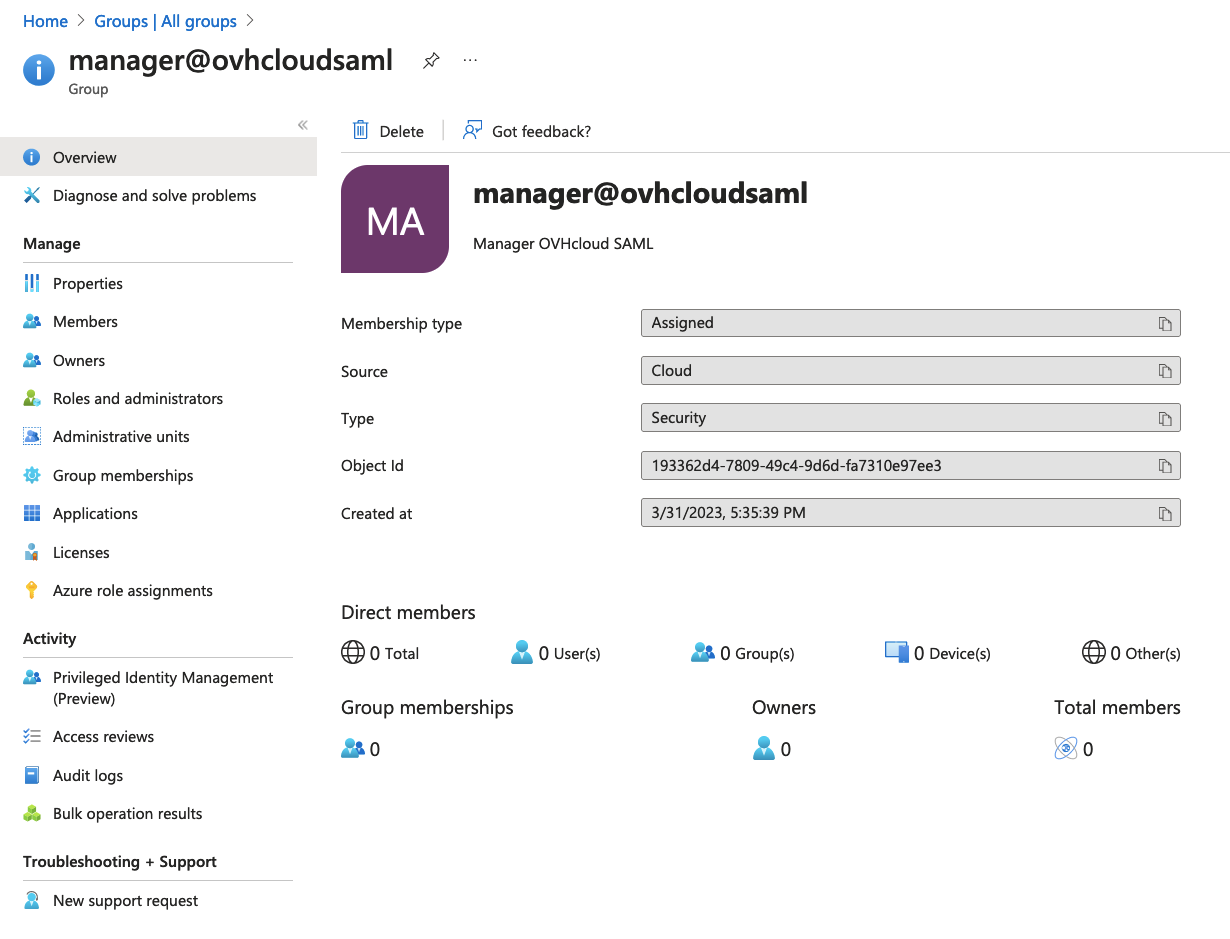
Add it by clicking on the Declare a group.
Fill in the fields, then click on the Confirm button.
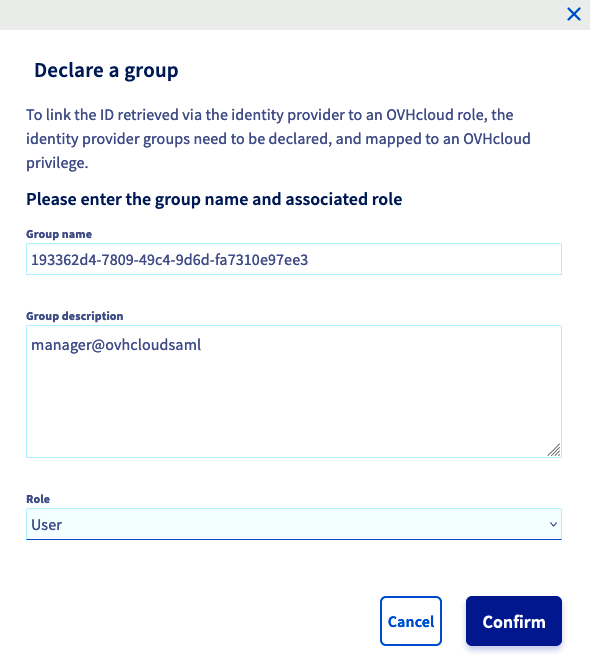
The created group should appear on the list.
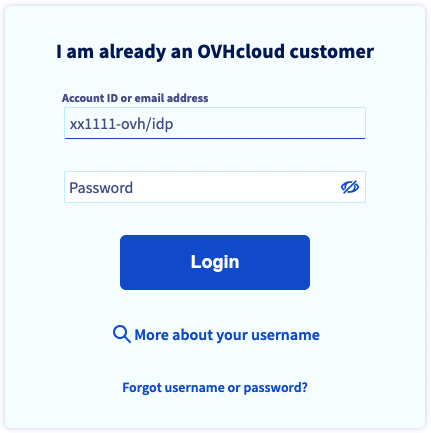
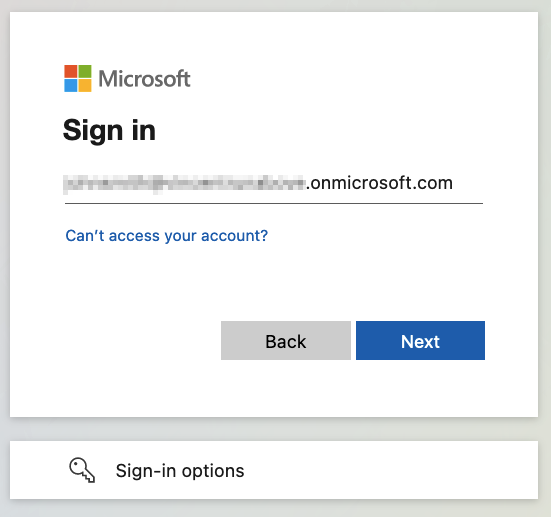
On the OVHcloud login page, enter your NIC handle followed by /idp without entering a password, and click the Login button.
You are then redirected to your Azure AD application login page. Select Use another account.
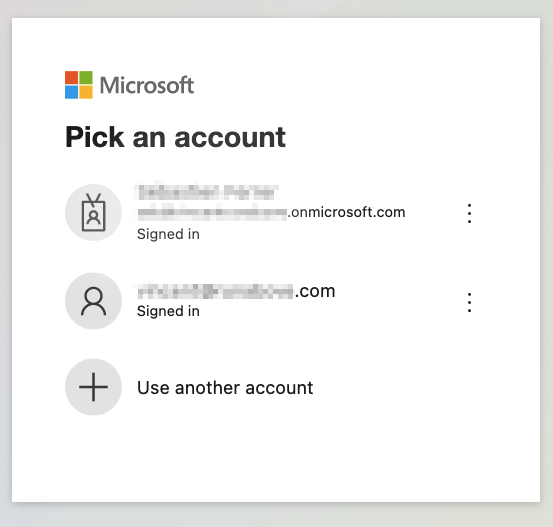
Enter the Azure AD application user email and click on the Next button.
Enter the Azure AD application user password and click on the Sign In button.
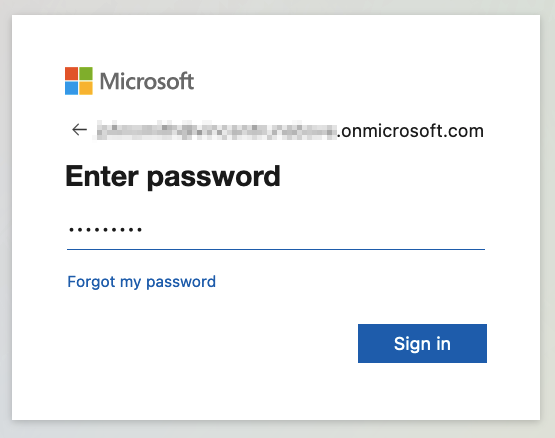
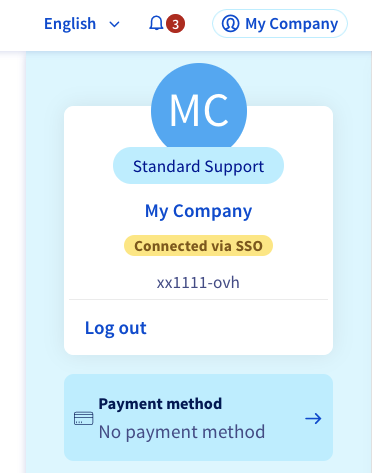
You are now logged in with the same NIC handle, but via your Active Directory user and using your Azure AD application SSO.
Join our community of users on https://community.ovh.com/en/.
Please feel free to give any suggestions in order to improve this documentation.
Whether your feedback is about images, content, or structure, please share it, so that we can improve it together.
Your support requests will not be processed via this form. To do this, please use the "Create a ticket" form.
Thank you. Your feedback has been received.
Access your community space. Ask questions, search for information, post content, and interact with other OVHcloud Community members.
Discuss with the OVHcloud community